What Is Ransomware Protection Software?
Ransomware protection software is a category of security tools to prevent, detect, and mitigate ransomware attacks. These attacks typically involve malware that encrypts files or entire systems, demanding payment for decryption keys. Ransomware protection solutions use a combination of proactive and reactive techniques to safeguard IT environments. The core goal is to block malware from gaining a foothold and, if a breach occurs, detect unusual behavior quickly enough to limit damage and support rapid recovery.
A ransomware protection solution integrates several layers of defense. It employs continuous monitoring, detection algorithms, ransomware backup stratgies and recovery mechanisms, endpoint security, and automated incident response. Modern solutions adapt to evolving ransomware tactics, such as fileless attacks or those that disable traditional security tools. However, most vendors specialize in either prevention/detection OR recovery resilience.
The effectiveness of ransomware protection software hinges on its ability to identify threats early, stop them before they cause widespread harm, and ensure that critical data can be restored without capitulating to ransom demands.
In this article:
- Key Capabilities of Modern Ransomware Protection Software
- Notable Ransomware Protection Software Focusing on DR
- Notable Ransomware Protection Software Focusing on Detection and Response4
Key Capabilities of Modern Ransomware Protection Software
Ransomware Protection Focused on Backup and Recovery
This category ensures data survivability, immutability, and rapid recovery, even when detection and prevention controls are bypassed.
- Automated backups with isolated storage: Performs frequent, policy-driven backups to locations isolated from production environments. Isolation prevents ransomware from encrypting or deleting backup data during an attack.
- Immutable storage using Amazon S3 Object Lock: Enforces write-once, read-many (WORM) protection for backup objects stored in Amazon S3. Retention periods prevent deletion or modification, even by administrators, ensuring backups remain intact throughout ransomware incidents.
- Governance and compliance immutability modes: Supports governance mode for controlled administrative overrides and compliance mode for absolute immutability. Compliance mode ensures objects cannot be altered or deleted until retention expiration, meeting strict regulatory requirements.
- Highly secure snapshot vaults: Adds protection beyond native cloud snapshots by copying them to hardened vaults with restricted deletion rights. Cross-region and cross-account isolation prevents attackers from erasing recovery points, even if production credentials are compromised.
- Cross-account disaster recovery ransomware-proofing: Replicates backups and recovery resources to a separate AWS account with strict IAM boundaries and independent encryption keys. This creates a clean recovery domain unaffected by ransomware in the primary environment.
- Cross-cloud disaster recovery ransomware-proofing: Extends isolation across cloud providers such as AWS, Azure, and Google Cloud. Independent credentials, APIs, and immutable storage options ensure ransomware cannot propagate across platforms, preserving at least one viable recovery environment.
- Fast recovery and orchestration: Enables point-in-time restores and automated recovery workflows that rapidly bring critical workloads back online. Integrated orchestration reduces recovery time objectives (RTO) and supports regular disaster recovery testing.
Ransomware Protection Focused on Detection and Response
This category concentrates on early identification, containment, and rapid mitigation of ransomware activity before widespread damage occurs.
- Behavioral detection and anomaly detection: Continuously analyzes user, system, and network behavior to identify deviations from normal activity. Machine learning establishes baselines and flags suspicious actions such as mass file encryption, unusual privilege escalation, or abnormal file access patterns. These techniques enable detection of zero-day ransomware variants that signature-based tools often miss.
- Real-time monitoring and prevention: Provides always-on visibility into file operations, process execution, memory activity, and network traffic. Prevention mechanisms block malicious actions in real time, such as unauthorized encryption attempts, script execution, or disabling of security controls, stopping ransomware before it can complete its payload.
- Endpoint protection and hardening: Secures laptops, desktops, and servers through layered defenses including exploit prevention, memory protection, and application control. Hardening reduces attack surface by enforcing least-privilege access, disabling unnecessary services, and preventing lateral movement within the environment.
- Automated response and containment: Automatically isolates infected systems, terminates malicious processes, and severs command-and-control communication the moment ransomware behavior is detected. This minimizes the blast radius and reduces reliance on manual intervention during high-pressure incidents.
- Rollback and file-level restoration: Rapidly restores affected files or systems to a known-good state using snapshots or shadow copies. Rollback operates surgically on impacted assets, significantly reducing downtime compared to full system restores.
- Anti-phishing and web filtering integration: Blocks common ransomware entry points by scanning emails for malicious attachments and links, and preventing access to high-risk or newly registered domains. This disrupts the attack chain before ransomware ever reaches an endpoint.
Related content: Read our guide to ransomware prevention
Notable Ransomware Protection Software Focusing on DR
1. N2W
N2W is a cloud-native backup and disaster recovery platform built specifically for AWS and Azure environments. Rather than focusing only on detecting ransomware, N2W eliminates ransom leverage entirely by ensuring your data is immutable, isolated, and instantly recoverable.
Key ransomware protection capabilities include:
- Cross-account and cross-cloud isolation: Backups are replicated into a separate AWS account, Azure subscription, or Wasabi, creating a clean recovery domain with independent credentials and encryption keys. Even if production credentials are compromised, recovery points remain protected.
- Immutable backups (S3 Object Lock & Wasabi Compliance Lock): N2W supports immutable storage in Amazon, Azure, and Wasabi repositories, preventing deletion or modification (even by privileged users) until retention periods expire. This creates a true WORM-based protection layer.
- Air-gapped disaster recovery accounts: You can create a dedicated DR account where no one has permission to delete backups. Combined with MFA, encryption keys, and strict IAM boundaries, this forms a practical air gap inside your cloud architecture.
- One-click disaster recovery orchestration: Recover full environments—including VPCs, VPNs, routing tables, load balancers, and EKS clusters—in the correct order. N2W allows orchestrated failover and failback in just a few clicks, minimizing RTO and operational complexity.
- Automated DR drills & recovery scenarios: Run scheduled or on-demand disaster recovery tests without affecting production. Validate that backups are not just stored, but actually restorable.
- AWS EKS Backup & Recovery: Policy-driven protection for Kubernetes namespaces and full clusters, with recovery to the same or a different cluster (ideal for ransomware rollback or cross-cluster migration).
- Data lifecycle cost optimization: Reduce storage costs with automated archiving, multiple retention policies in one rule, and instant “Run-Now” cleanup to eliminate unnecessary generations.
Why it matters:
- Detection tools try to stop ransomware.
- N2W ensures that even if detection fails, your business doesn’t.
- Prevention lowers risk.
- Immutable, isolated recovery removes ransom leverage.
2. Backblaze
Backblaze offers a ransomware protection and disaster recovery solution centered around secure, immutable cloud storage. Its platform ensures rapid data recovery while protecting backups from tampering, deletion, or encryption by ransomware.
Key features include:
- Immutable storage with object lock: Prevents backup data from being modified or deleted using write-once, read-many (WORM) technology.
- AES-256 encrypted backups: Secures data at rest with server-side encryption to protect it from unauthorized access.
- Always-hot storage: Designed for fast retrieval without cold-tier delays. Note: Backblaze B2 does charge egress (unless under certain programs).
- Disaster-ready replication: Supports automated multi-location replication for resilient and redundant storage.
- Recovery testing support: Allows up to 3 times stored data in monthly egress to validate backups and test recovery procedures.
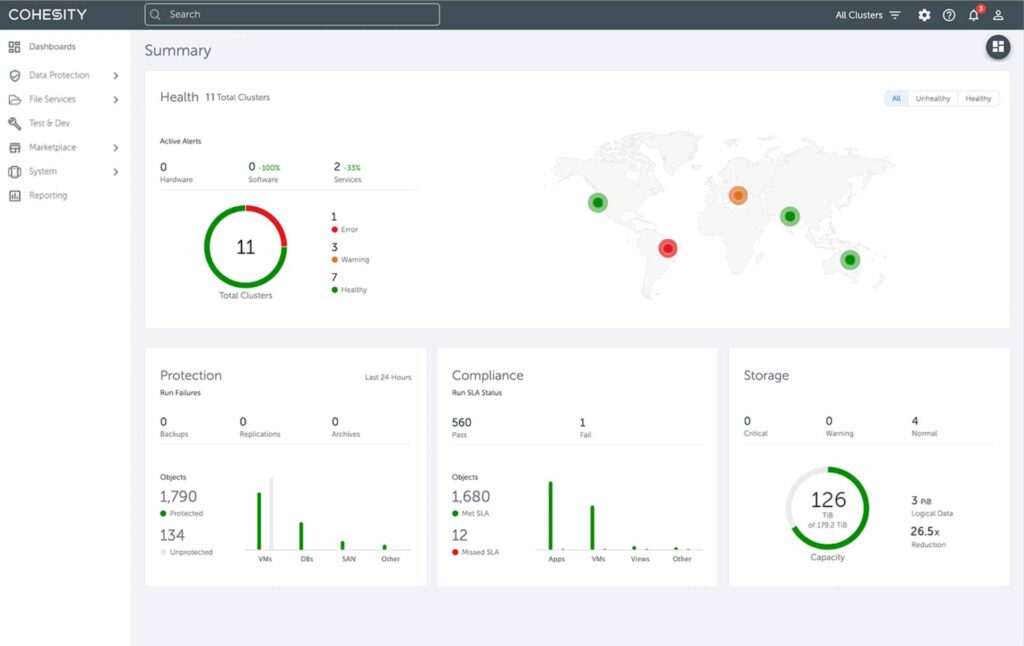
3. Cohesity
Cohesity delivers a ransomware recovery and resilience platform that combines AI-powered threat detection, zero trust architecture, and instant recovery capabilities. It defends critical data through multilayered protection mechanisms, from immutable backup snapshots to automated threat intelligence and scanning.
Key features include:
- Immutable backup with DataLock: Protects backup data using write-once, read-many (WORM) snapshots that cannot be altered or deleted by ransomware or malicious insiders.
- Zero trust security framework: Implements multi-factor authentication (MFA), role-based access control (RBAC), and quorum-based approvals to prevent unauthorized changes and limit attack surfaces.
- AI/ML-based threat detection: Uses behavioral analytics, anomaly detection, and curated threat feeds to identify ransomware activity and indicators of compromise (IOCs) early.
- Integrated threat scanning: Automatically scans backup data for malware before recovery, helping ensure restored systems are clean and secure.
- Instant recovery at scale: Enables near-instant recovery of virtual machines, NAS data, and databases using fully hydrated snapshots, minimizing downtime.
Notable Ransomware Protection Software Focusing on Detection and Response
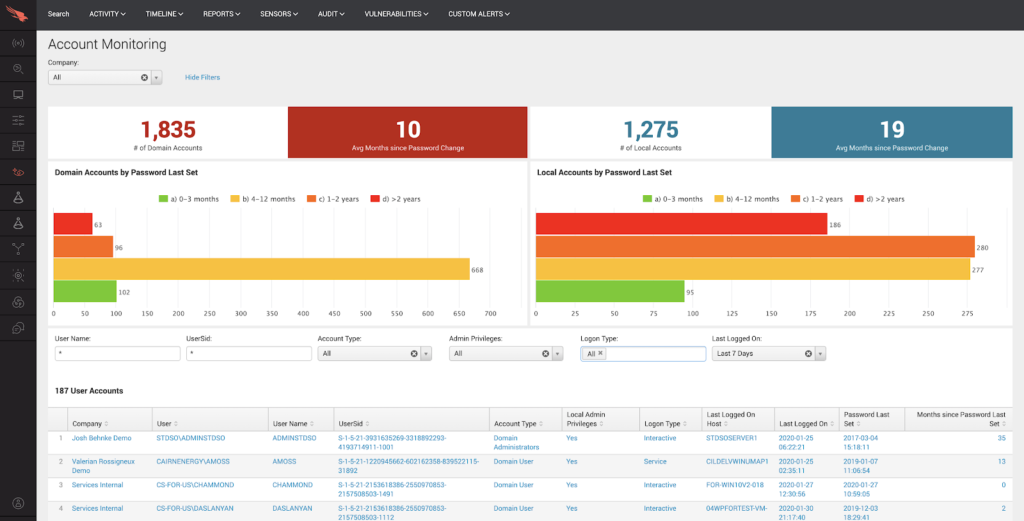
4. CrowdStrike Falcon

CrowdStrike Falcon is a cloud-native endpoint protection platform that defends against ransomware with AI-powered prevention, real-time monitoring, and expert-led threat hunting. It delivers visibility into ransomware activity across endpoints while blocking both known and unknown threats before they cause damage.
General features include:
- AI-powered threat prevention: Uses artificial intelligence and threat intelligence to block both known and unknown ransomware before it can execute.
- Real-time visibility: Continuously monitors endpoints to detect suspicious behavior and attack indicators across the enterprise.
- Expert-driven threat hunting: Employs a team of dedicated hunters who proactively search for emerging threats and disrupt attacks before they unfold.
- Validated protection performance: Achieved 100% ransomware protection in SE Labs’ enterprise testing, demonstrating effectiveness in both direct and complex, real-world attack simulations.
- Security readiness exercises: Offers tabletop drills, red team/blue team simulations, and adversary emulation to test defenses, uncover gaps, and strengthen incident response.
Ransomware protection features include:
- Proactive ransomware blocking: Combines machine learning, behavioral analytics, and threat intelligence to stop ransomware before it causes harm.
- Endpoint detection and response (EDR): Provides detailed visibility into endpoint activities, including process behavior and adversary tactics.
- Adversary mapping and insights: Identifies threat actors targeting specific industries and provides intelligence to guide defenses.
- Isolate and contain infections: Enables security teams to respond immediately by isolating affected systems and containing ransomware spread.
- Continuous protection across platforms: Ensures persistent security coverage for both desktop and mobile endpoints through the cloud-native Falcon platform.
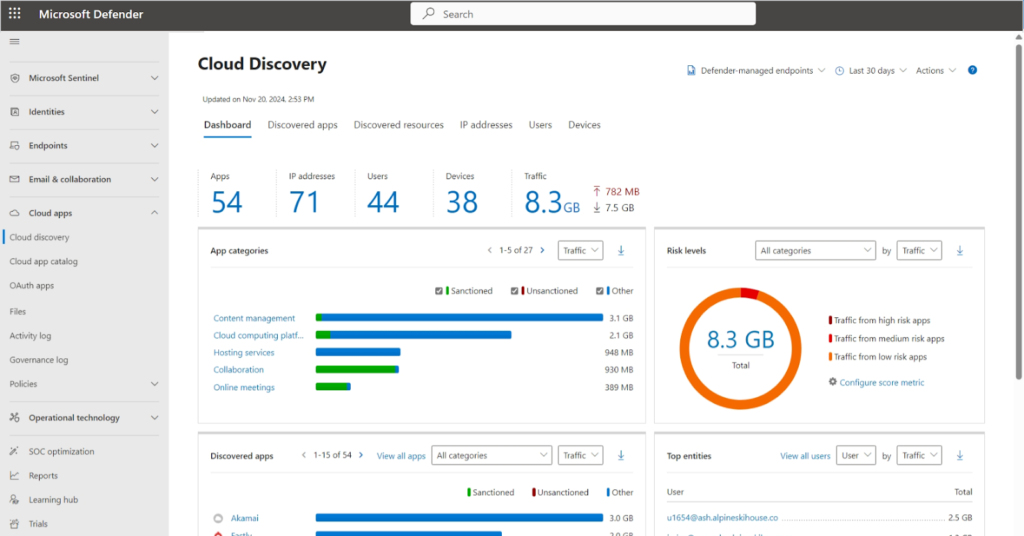
5. Microsoft Defender for Endpoint

Microsoft Defender for Endpoint provides a multilayered defense approach to ransomware by combining prevention, detection, investigation, and automated response. Built on a zero trust foundation, it uses cloud-delivered protection, configurable security baselines, and safeguards like tamper protection to reduce attack surfaces and block ransomware at multiple stages.
General features include:
- Built-in protection defaults: Automatically applies a set of secure configuration defaults, including tamper protection and attack surface reduction rules, to defend against ransomware and other threats as soon as devices are onboarded.
- Cloud-delivered threat prevention: Uses Microsoft’s cloud-based protection engine to identify and stop threats, with updates driven by global intelligence.
- Attack surface reduction rules: Enables standardized rules that reduce exploitable entry points by blocking behaviors commonly associated with ransomware, such as executing scripts or launching suspicious macros.
- Tamper protection: Prevents malicious apps or attackers from disabling Microsoft Defender settings, providing a resilient layer of protection that is enforced even against administrative changes.
- Cross-platform and policy-based control: Allows centralized configuration through Microsoft Intune or Configuration Manager, enabling enforcement of custom security policies across Windows and macOS devices.
Ransomware protection features include:
- Tamper-resilient configuration management: Locks down security settings to prevent unauthorized changes, ensuring ransomware cannot weaken or disable defenses.
- Automatic application of secure settings: Ensures protection features like tamper protection and network protection are active by default, without requiring manual configuration.
- Customizable security posture: Lets organizations override built-in defaults with their own policies to meet business needs while maintaining a strong defense against ransomware.
- Role-based access for changes: Enforces least-privilege principles by requiring specific roles, such as Security Administrator, to modify critical settings, reducing risk of misconfiguration or compromise.
- Integration with Microsoft Endpoint Manager: Supports policy-driven deployment and enforcement of ransomware protection controls using Intune or other MDM solutions.
NOTE: Advanced ransomware capabilities require Defender for Endpoint Plan 2.
6. Sophos Intercept X

Sophos Intercept X provides ransomware protection by combining behavioral detection, exploit prevention, and automated rollback. It covers various ransomware threats, including remote encryption and zero-day variants, using techniques to stop attacks before they encrypt data. Features include CryptoGuard, anti-exploitation defenses, and synchronized security across endpoints and firewalls.
General features include:
- Synchronized security: Enables real-time sharing of threat intelligence between endpoints and firewalls to automatically isolate infected systems and accelerate response.
- Zero-touch endpoint defense: Protects against threats with minimal manual intervention by automatically detecting and responding to attacks.
- Global threat operations support: Backed by Sophos X-Ops, which provides 24/7 threat monitoring and response capabilities.
- Full application visibility: Offers visibility into all applications on the network to help detect unusual behavior and hidden threats.
- Phishing and web threat protection: Secures endpoints against common ransomware delivery methods, including phishing emails, malicious attachments, and unsafe websites.
Ransomware protection features include:
- CryptoGuard rollback technology: Detects unauthorized file encryption in real time and automatically restores affected files to their original state, eliminating the need to pay ransoms. Note: rollback works for supported file systems and scenarios.
- Remote ransomware protection: Stops ransomware from encrypting files over the network, even if the attack originates from a compromised external device.
- Exploit prevention: Blocks over 60 known exploit techniques used by attackers to deliver ransomware, with no need for custom rule configuration or tuning.
- Behavior-based detection: Identifies ransomware activity by analyzing runtime behaviors, including those of previously unknown or polymorphic strains.
Conclusion
Modern ransomware protection requires more than antivirus or basic backups. Prevention and detection tools reduce risk—but they cannot guarantee immunity.
True resilience comes from layered defense:
- Behavioral monitoring to detect anomalies early
- Automated containment to limit blast radius
- Immutable, isolated backups to eliminate ransom leverage
- Orchestrated disaster recovery to restore operations in minutes—not days
As ransomware tactics evolve, organizations must shift from “How do we stop every attack?” to “How do we recover instantly if one succeeds?”