What is NIST?
National Institute of Standards and Technology (NIST) guidelines come from a United States government agency which operates within the Department of Commerce. Although the department was founded over a hundred years ago, they’ve maintained their goal of developing new safety and security standards over the years for various fields such as cybersecurity, backup and recovery and others related to modern tech.
NIST guidelines have most recently focused on organizational security, personal data and defending teams against an ever-growing wave of cyber threats. The original NIST Cybersecurity Framework (CSF) was first introduced over a decade ago and has become the go-to baseline for many global organizations.
Particularly those institutions that sit outside the EU and fall outside the scope of the required (and similar) NIS2 standards can benefit by implementing NIST due to it being a high-level, voluntary framework. NIST has no pass or fail, making it an ideal starting point for building a security posture that can then be adapted to meet other mandated compliance requirements. For organizations that want to go further, NIST does offer an official validation process where companies can formally submit their architecture and processes for recognition.
NIST Updates
Cybersecurity is one of the most rapidly evolving fields in technology and threats grow more sophisticated by the day. Defenses we build to counter them must keep pace. As a result, NIST, like most compliance frameworks, continuously reviews and updates its recommendations to reflect the latest risks and best practices.
NIST had a major update in February 2024, the first major overhaul in a decade since its inception and they are set to release another update this year which plan to tackle specific industry guidelines.
Most changes were made in particular to the ‘Protect’ pillar which emphasized the importance of infrastructure resilience with future-forward methods liked immutable backups (more on this below). The entire NIST framework (NIST CSF 2.0) can be found on the official website.
The Six Pillars of NIST
NIST CSF 2.0 is built around six core pillars, each designed to address a distinct layer of cybersecurity risk, together forming a comprehensive, end-to-end framework for protecting an organization from modern threats. They are:
- Detect: how your company monitors intrusions, anomalies and security events.
- Identify: how assets are managed, risk and your data landscape is assessed.
- Respond: tasks that must be taken care immediately after a security incident
- Protect: how your organizations cover their risk for future attacks.
- Recover: resilient, proper backup, recovery and disaster recovery
- Govern: how your enterprise implements “control”-oriented capabilities, how you measure success, review and plan for the future
How to approach the NIST requirements with N2W
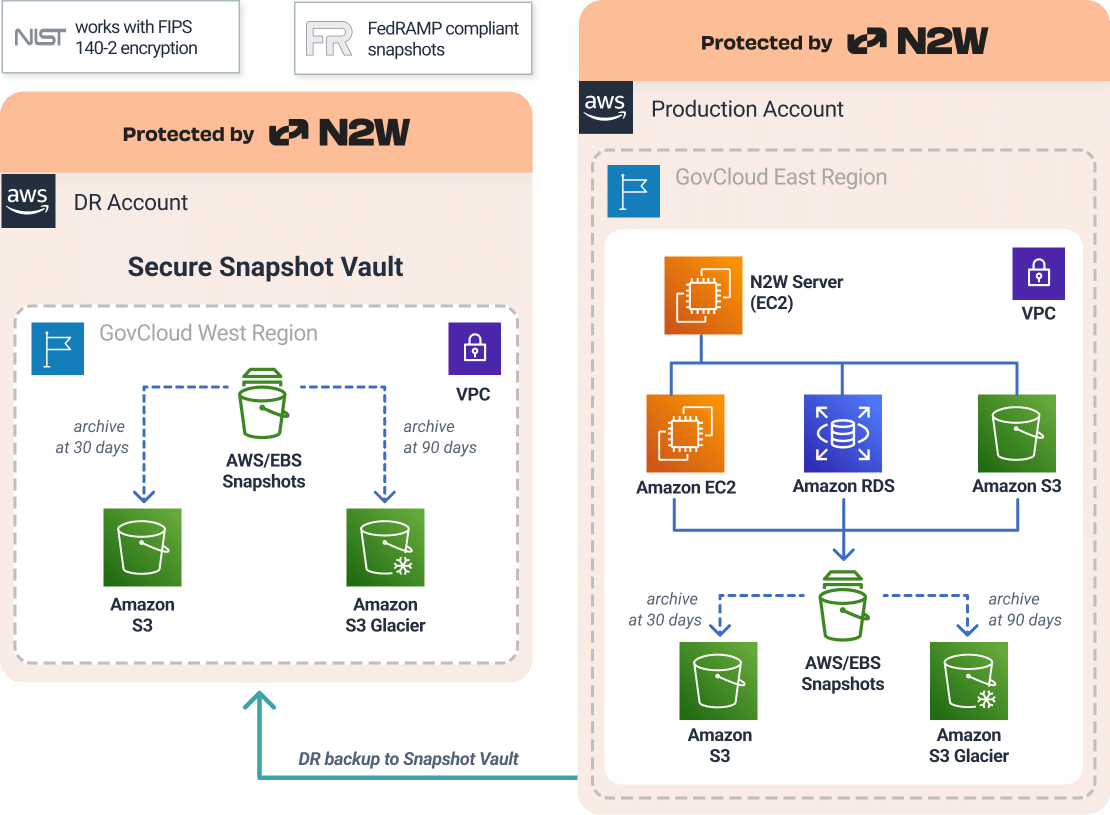
For N2W customers, meeting NIST guidelines doesn’t require heavy lifting at all. With out-of-the-box, compliance-ready features, organizations can significantly reduce security risk and protect their data from day one. Below is a real-world architecture example showing how one of our customers validated their NIST data protection posture using N2W, successfully implementing best practices across all six pillars directly from the N2W console, freeing their team to focus on the business while their security runs on autopilot.
Ten N2W core rapid-compliance capabilities and the corresponding NIST pillar that they satisfy:
1. NIST on Backup and Recovery Drills (Protect, Recover and Govern Pillars)
NIST is very explicit about backup and recovery testing requirements (specifically under NIST SP 800-53 CP-9 and its corresponding enhancements). NIST states that organizations must run backup and disaster recovery drills at a frequency that is defined by the organization in order to verify critical data can be retrieved. CP-9(2) states that organizations must use a sample of their backups to demonstrate a healthy restore.
N2W Recovery Scenarios not only makes backup and recovery drills automated and effortless, it ensures your entire environment can be restored and up and running back to a healthy production state. N2W can:
- regularly execute scheduled recovery scenarios for multiple resources across selected workloads
- restore prioritization of as many resources as necessary
- validate full system functionality by verifying configurations, and metadata dependencies, guaranteeing a fully operational production-ready state.
- provide documented, audit-ready evidence with general and detailed success reporting
- reduce human error and operational risk with standardized recovery workflows
2. NIST on Encryption (Protect Pillar)
NIST CP-9(8) states that cryptographic protection for backups must be implemented. Encryption mechanisms must protect the integrity of all backup data.
With N2W, encryption is implemented both at rest and in transit with customer-controlled unique keys. This is typically the gold standard of data encryption, the same level used by governments and financial institutions.
3. NIST on Immutable Backups (Protect Pillar)
NIST specifies some form of immutability in two specific sections: CP-9 Enhancement: Dual Authorization which is also sometimes called “two-person integrity”. It means one single person alone cannot delete or destroy data, there needs to be an authorized person to approve this action. In addition, the 2024 update reinforced the fact that data protection must expand using immutable security methods, as well as other resilience implementations.
N2W backups are completely tamper-proof when immutability is implemented. N2W provides Compliance Locking immutability, the highest level of immutability using object lock and full encryption. Insider employees, malicious cyber actors, automated ransomware, even the root users cannot delete or alter your backups. They will be safe under the retention period of immutability selected.
4. NIST on Disaster Recovery (Respond, Protect, Recover and Govern Pillars)
NIST’s CP-9 enhancement defines Offsite Transfer – backup data must be transferred to an off-site, isolated storage site which corresponds with a backup frequency and a retention period that satisfies your organization’s Recovery Time Objectives (RTO) and Recovery Point Objectives (RPO). NIST also requiresRedundant Systems, meaning there should be a secondary backup system that will not interfere with production and will not disrupt any operations during restore.
Disaster Recovery with N2W can be performed across regions, account (AWS) and subscriptions (Azure) guaranteeing off-site, healthy backups that will not impact production at all when restoring. N2W also performs cross-cloud backups providing true geographic, vendor-isolated redundancy and protection against disasters or attacks on your primary environment/cloud.
5. NIST on Backup Frequency and Recovery Time
NIST SP 800-34 Rev. 1 (Contingency Planning Guide), defines minimum backup frequency and establishes RTO and RPO as part of your business impact analysis.
N2W allows for automated, frequent backups. Frequency is entirely flexible depending on the needs of the organization. N2W allows for backup frequency every five minutes in many customer cases, as compared to native tools that have typical limitations of 4 to 6 hours. This is key in minimizing the amount of data loss. RTO with N2W is near-zero, which native tools in many cases guarantee up to 24 hours.
6. NIST on Reporting
NIST SP 800-34 states that documentation and reviewing of all testing drills must take place for efficient auditing, communication and planning.
N2W will generate automated, comprehensive reports as well as detailed logs that auditors, compliance departments and C-level suite managers can access in minutes. All evidence can be provided with minimal effort, no scrambling to staple together from various consoles and the answer to ‘How do you know your recover actually works’ is answered immediately.
7. NIST on Governance (Govern Pillar)
NIST’s Govern Pillar was most recently added in 2024 to optimize how enterprises can establish full control of their data protection operations. NIST, with this pillar, is signaling that enterprises must have full, documented control over who owns their data, how it is protected, and who is accountable when things go wrong.
One of N2W’s most important differentiators is key ownership. N2W operates as an IaaS model, so our customers’ data never leaves their account, encryption keys are always under their control and there is no third party SaaS vendor that access or stores their data. Not even N2W can access a customer’s environment.
N2W also provides a single, easy-to-use dashboard to centralize and automate backup and recovery, enabling organizations to enforce consistent backup governance across thousands of workloads or a single mission-critical app. Multiple retention schedules per policy allow organizations to enforce data governance rules and meet regulatory and legal data retention requirements from a single management plane.
8. NIST on Strict Access Control (Protect, Respond & Recover Pillars)
NIST SP 800-53 defines how organizations should guarantee the principle of least privilege. This means that organizations must allow only authorized accesses for users that are necessary to accomplish assigned organizational tasks. All data protection actions, APIs, and automated processes should be granted only the minimum essential privileges required for operations.
Beyond protecting the data itself, N2W protects backup and DR accounts with multi-factor authentication (MFA), encryption keys, and strong password policies. This ensures that customers have layered security around the keys themselves.
When N2W is setup, organizations configure a custom IAM role in AWS and Azure. In addition this gives administrators full and precise control over who can log in and take any action with backup resources. This ensures access privileges follow the principle of least privilege.
9. NIST on Identifying Assets (Identity Pillar)
NIST’s Identify Pillar serves as the foundation of the entire CSF framework because you cannot protect what you cannot see. IT teams should have a complete, up-to-date picture of every resource that requires protection before they can effectively defend it.
N2W provides monitoring at multiple levels via an easy-to-use dashboard displaying key performance indicators for backups, disaster recoveries, volume usage, backups to S3, and other metrics.
N2W also allows for automated tagging, enabling organizations to automatically classify and label AWS and Azure resources based on business criticality, environment type, ownership, and compliance requirements. This ensures that every asset is accounted for, properly categorized, and tied to the right backup policies without manual intervention
N2W Recovery Scenarios prioritizes every single resource within the customer’s policy including the associated metadata, ensuring no pro-active assurance that no gaps are excluded when a real recovery must take place.
10. NIST on Detection (Detect Pillar)
NIST’s Detect Pillar mandates that organizations implement continuous monitoring capabilities to identify any security gaps in a timely manner.
N2W monitors backup job status and user immediately receives alerts on any failures, as well as daily backup summaries helping organizations maintain their RPO and RTO requirements while reducing manual oversight of backup operations. Automated backup scheduling ensures gaps in coverage are immediately visible, alerting teams to any missed or failed backup jobs before they become a liability
NIST’s MSP-Specific Guidance
NIST specifically calls out MSP’s in their Guide for Managed Service Providers to Conduct, Maintain and Test Backup Files. MSP’s manage backups on behalf of their clients. NIST stresses the importance of data protection for these entities because these are high-value targets. If there are gaps on control, multiple clients will be exposed at once. One single compromise for an MSP can mean catastrophic damage.
N2W is built for partners (MSPs and resellers) by not only providing them with a single console for complete control, visibility and multi-tenancy, it allows them to be true strategic partners, making it easy to implement compliance, disaster recovery and streamlined backup procedures.
Need Guidance? See where you stand with NIST
We’re happy to run a NIST compliance health check ensuring all gaps are closed. Contact us at info@n2ws.com and in the meantime, spin up a free trial.